 EZRentOut supports multiple login options. These include Google Account, Microsoft Account, LDAP and SAML providers. You can configure which login options to give to users from Settings → Company Settings → Authentication. In this post, we’ll discuss SAML.
EZRentOut supports multiple login options. These include Google Account, Microsoft Account, LDAP and SAML providers. You can configure which login options to give to users from Settings → Company Settings → Authentication. In this post, we’ll discuss SAML.
Users in your organization can access EZRentOut through SAML. No need for your users to remember separate credentials for EZRentOut. To start, enable SAML Integration from Settings → Add Ons.
What is SAML?
Security Assertion Markup Language (SAML) is an XML standard that enables a user to log on once to affiliated but separate websites. SAML creates end points that give an organization’s users a single URL to sign in and select the applications they are authorized to use. This provides an additional level of security and simplifies user authentication. One of the main components of SAML include assertions which are:
– Authentication assertion validates the user’s identity.
– Attribute assertion contains specific information about the user.
– Authorization assertion identifies what the user is authorized to do.
Why implement SAML?
Reasons include usability, directory integration and security. A user can access applications with a single click and allows to launch apps from SSO portals. In terms of security, SAML eliminates the use of passwords, centralizes access control and prevents illegal or unnecessary access from former employees.
How SAML works?
SAML SSO works by authenticating a user against the company’s identity provider, say OneLogin or Okta. It transfers the user’s data from one destination to another i.e. from identity provider to the service provider. In this case, EZRentOut is your service provider.
Your identity provider authenticates the user by creating an XML document containing user’s credentials and email address. It then signs it using the certificate and sends back the information to EZRentOut.
Some of the Identity Providers supported by EZRentOut are:
– OneLogin
– Okta
– Centrify
– Simplify
– Auth0
Configuring an identity provider for EZRentOut
Here, we will be using OneLogin as an example, which provides SSO and identity management for cloud based applications. With OneLogin, users can enable enterprise-grade SSO over the cloud, allowing all end-users to connect with included SaaS services. For other providers, the steps are similar.
1. Adding the App
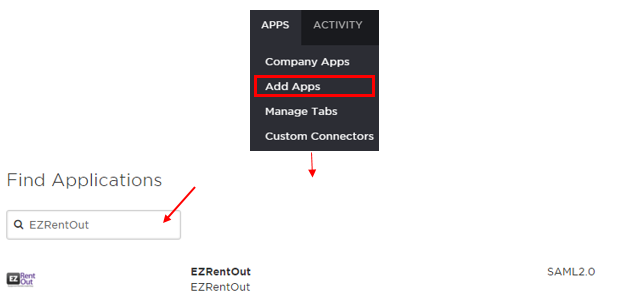
Find ‘EZRentOut’ from the OneLogin page, go to Apps → Add Apps → Find Applications.Click ‘Save’ and your OneLogin account is ready to be integrated with EZRentOut app. From the Company Apps, you can view all saved applications in your OneLogin account.
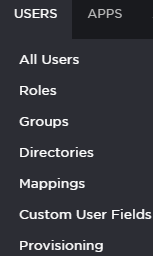
2. Making sure users have the correct attributes
Your SAML users should have the attributes for Last Name and Email Address, which are required by EZRentOut to retrieve and validate users.These attributes can be mapped to Last Name and Email addresses of members in EZRentOut settings.
Configuring EZRentOut for SAML Integration
Once you have set up an EZRentOut app on your preferred SAML identity provider, configure the settings in EZRentOut from Settings → Add Ons → SAML Integration. Again, we have used OneLogin as an example.
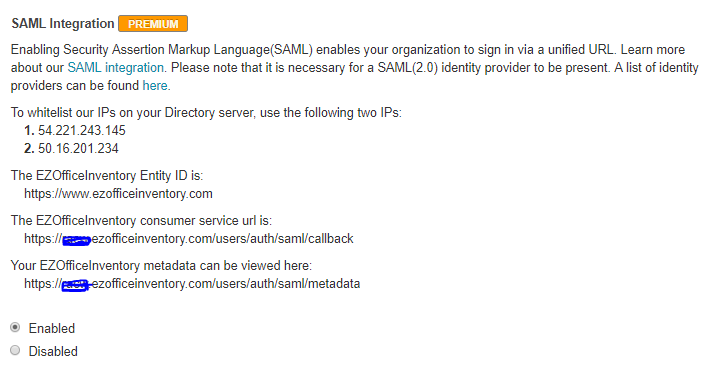
1. Whitelisting the IPs on SAML
Some identity providers require IPs to be whitelisted. Make sure that the following two IPs are whitelisted in your SAML settings:
i. 52.2.223.197
ii. 54.208.123.254
2. Add EZRentOut consumer service URL to your SAML Settings
The EZRentOut consumer service url can be obtained from Settings → Add Ons → SAML Integration:
https://<Your Company Subdomain>.ezrentout.com/users/auth/saml/callback
3. Fill in the configuration settings
The following information needs to be configured in your EZRentOut’s account (see image to identify the fields):
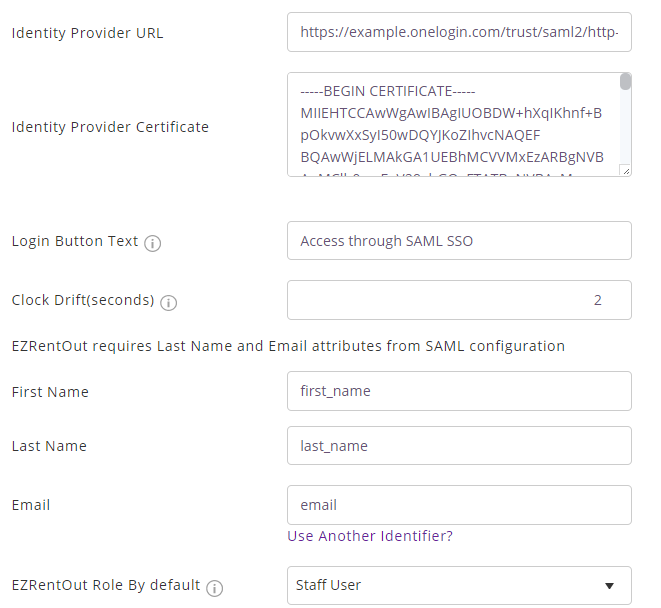
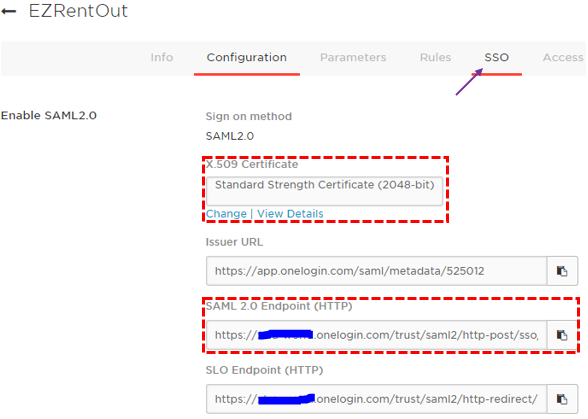
1. Unique Identity Provider URL: Find and copy your Identity Provider URL from Apps → Company Apps → EZRentOut → SSO tab → SAML 2.0 Endpoint (HTTP) (see the image below). You will be required to paste this link in ‘Identity Provider URL’ field while configuring EZRentOut for SAML Integration.
2. Identity Provider X.509 Certificate: Unique for every account owner, this certificate is provided by the identity provider. In OneLogin, find and copy your X.509 certificate from Apps → Company Apps → EZRentOut → SSO tab → X.509 Certificate (see image above). EZRentOut will use the certificate to validate the response from your identity provider letting the user to login in using SAML.
Note: Makes sure to follow the below format for the certificate when pasting it in the certificate field so EZRentOut validates your Identity provider’s certificate without any error. It’s as follows:
—–BEGIN CERTIFICATE—–
your certificate details here
—–END CERTIFICATE—–
3. Label Login Button Text: By default it’s labeled as ‘Access through SAML SSO’. You can rename it to any text preferable to you e.g. Access using Acme Corp Login.
4. Attributes required for SAML configuration: Last Name and Email attributes need to be present for EZRentOut. These attributes/parameters should be sent over to EZRentOut from your identity provider. In OneLogin, they can be viewed from Apps → Company Apps → EZRentOut → Parameters. Also, map these parameters in EZRentOut. If your Last Name attribute in SAML is last_name, then fill in ‘last_name’ against the Last Name field. Same goes for the Email.
5. Scroll down to the end of the Add Ons page in EZRentOut settings, and click ‘Update’. You now have a SAML enabled EZRentOut account.
Login Experience
The following takes place when a user tries to login to a SAML enabled EZRentOut account:
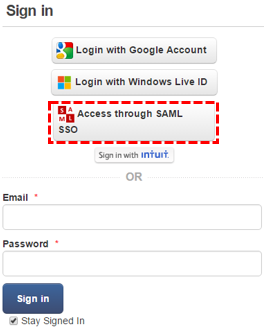
When the user goes to your EZRentOut portal, they see the SAML access option. See image below.– Clicking ‘Access through SAML’ takes a user to SAML Provider’s page for authentication.
– If the user is already signed in to your SAML Provider’s account (e.g. OneLogin) they’ll directly land into the EZRentOut portal.
– The email address of the user determines which EZRentOut member they are.
– A user who isn’t added to an EZRentOut’s account under More tab → Users, but accesses that EZRentOut account for the first time via SAML, is added as a new staff user.
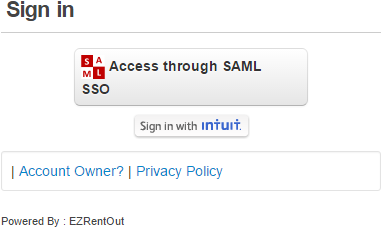
Note: In a scenario, where users might want to use SAML as the only authentication option in EZRentOut, you can disable other options from Company Settings → Authentication. See image below how the login page looks later.
For LDAP integration with EZRentOut, click here
Supported by ADFS
The SAML integration is supported by ADFS, so you can rest easy knowing you get to enjoy all the benefits that ADFS has to offer, such as:
- Secure account provisioning
- Hassle-free account credential management
- Easy account management
- Simplified account deactivation
- Effective change management
Share your Queries
Log into your account to try this out and let us know what you think at info@ezo.io.
FAQs
Q. How to verify the information while setting up SAML Integration for EZRentOut?
A. Following are some of the URLs that you may require during the configuration process:
–Sign On URL: https://<Your Company’s Subdomain>.ezrentout.com/users/sign_in
–Identifier/Issuer: https://www.ezrentout.com (Note: Do not enter your subdomain with it)
-Assertion Consumer Service URL: https://<Your Company’s Subdomain>.com/users/auth/saml/callback
Q. What if the Identity Provider asks for 4 attributes e.g. First Name, Last Name, Email and Principle Name? Will it matter as EZRentOut only looks for First Name, Last Name and Email?
A. The extra attribute will not be an issue. However, while configuring, you’d most probably have to map the exact attribute names of the first name, last name and email fields that are provided by the Identity provider in the Settings -> Add Ons page.
Q. Sensitive information exchanged in the SAML assertion?
A. No, only the email address is sent.
Q. How to paste your SAML SSO Certificate?
A. During the EZRentOut’s configuration process, paste the certificate in the field in between the following marks:
—–BEGIN CERTIFICATE—–
Paste certificate details here
—–END CERTIFICATE—–
Q. Someone at your organization tried accessing your EZRentOut portal through SAML, but could not log in. To fix this, verify that your integration has been set up correctly.
A. A common issue is not having Last Name and Email attributes configured in your SAML Set Up. To diagnose this:
1) Make sure EZRentOut is getting the Last Name and Email for members. The relevant options are available under Settings → Add Ons → SAML
2) Look for typos in SAML Attribute Names added in EZRentOut Settings. For example, if your SAML Attribute for Last Name is last_name, it should be entered as such.
3) In most cases, the parameters/attributes are mapped in your preferred identity provider configuration settings, otherwise your service provide will ask you to map them.






